Enhancing Trust with IBM Vault's Public Certificate Integration
For many enterprises, certificate management tends to be a fragmented nightmare. Manual processes overburden security teams, especially when it comes to handling X.509 certificates for external public trust. This pain point becomes even more amplified in dynamic environments, where agility and security are paramount. The recent enhancements to HashiCorp Vault—now branded as IBM Vault—can signal a significant shift in the approach to managing certificates across internal and external infrastructures.
Unpacking Certificate Management Challenges
The crux of the issue lies in the dual-track management of certificates. While Vault’s private PKI has streamlined and automated many internal processes, organizations often find themselves reverting to outdated, manual methods when facing external requirements. This disjointed approach leads to multiple headaches:
- Operational Overhead: Without direct integration for public certificate authorities, security teams are burdened with repetitive tasks such as manually navigating CA portals. This manual intervention is fraught with risks, often leading to errors such as missed renewals.
- The Outage Clock: Every manual request represents a time bomb. Organizations frequently lack a centralized dashboard to keep track of expiration timelines, resulting in unexpected downtime for critical services when certificates expire.
- Siloed Governance: Managing public and private certificates with separate tools complicates governance frameworks and compliance checks, making it increasingly difficult to enforce consistent security protocols and maintain audit trails for frameworks like NIST or PCI DSS.
- External Limitations: While private CAs serve internal needs, they fall short in public-facing operations. This inconsistency limits Vault's effectiveness in multi-cloud and hybrid scenarios where external validation is a must.
Centralizing PKI Automation
The recent improvements to Vault address these challenges head-on by enabling organizations to integrate public CAs into their existing workflows. This integration effectively turns Vault into a comprehensive tool for managing the entire lifecycle of certificates. By acting as a central orchestrator, Vault securely manages CA credentials while streamlining the complex validation processes necessary for public certificate issuance.
This means developers can request certificates trusted by public networks using the same APIs and workflows they already employ for internal certificates. The outcome? A centralized view, eliminating manual silos and enabling security teams to oversee their entire certificate landscape seamlessly.
Mechanics of Orchestrating Public Trust
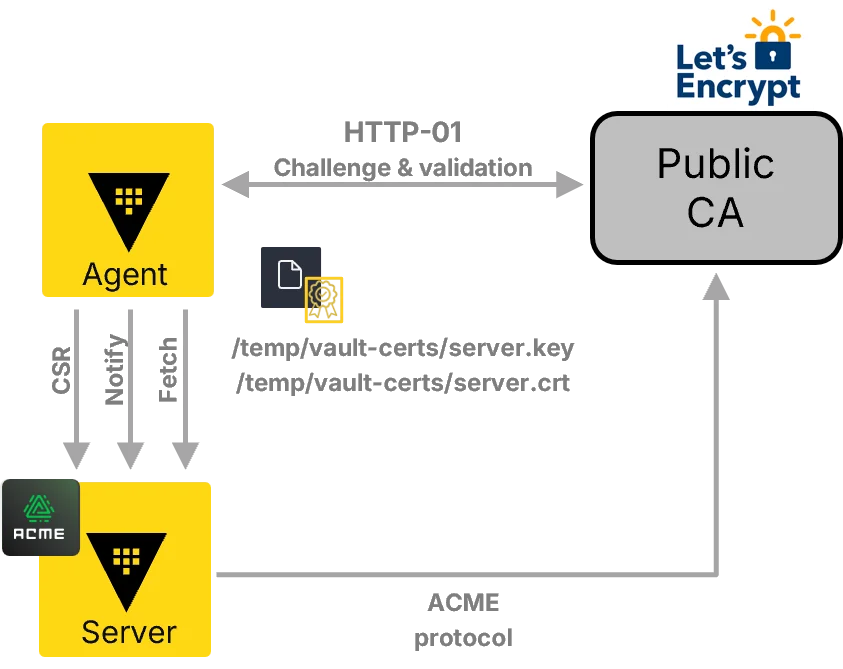
The underpinnings of this new functionality revolve around the Automated Certificate Management Environment (ACME) protocol, providing a vendor-agnostic framework that integrates various public CA needs.
Seamless Integration with Leading CAs
Vault now includes support for major public certificate authorities, enriching organizations’ capabilities. This integration currently covers:
- Let’s Encrypt
- DigiCert
- GlobalSign (in beta)
- Sectigo (in beta)
Vault Agent as the Orchestrating Hub
The newly enhanced Vault Agent serves as the primary facilitator, managing communication between Vault and public CAs while addressing domain validation requirements. In its initial rollout, this feature supports the HTTP-01 challenge, which automates domain ownership verification via HTTP, a crucial step for public certificate issuance. Future updates promise support for the DNS-01 challenge, catering to wildcard certificates and scenarios where web accessibility is limited.
Streamlined Workflows Across Teams
The integration empowers security and platform teams to efficiently manage public certificates directly within the Vault ecosystem, allowing for:
- Easy setup: Securely configure connections with public CAs using built-in Vault capabilities.
- Instant requests: Developers can request and download public certificates through Vault’s APIs, CLI, or UI, simplifying the issuance process.
- Controlled renewal: Teams maintain authority by manually renewing public certificates through Vault.
- Instant revocation: If any integrity issues arise, public certificates issued via Vault can be revoked promptly, ensuring that external security remains robust.
- Terraform integration: Leverage the updated Terraform Vault provider for full automation in setting up and managing public CA integrations.
Rethinking Security Strategy with Vault
With the expansion of its PKI capabilities, Vault seeks to redefine security management for enterprises. The integration of public CA management into Vault's ecosystem offers a streamlined approach that minimizes manual efforts while enhancing security measures across the board. Instead of oscillating between automation and public trust, organizations now have a unified solution.
If you’re a decision-maker or a practitioner facing the complexities of certificate management, this new functionality could be pivotal in mitigating risks associated with outages and manual oversight. The ability to seamlessly integrate public trust into your security framework is not just a convenience; it's a vital step toward a more resilient and compliant digital environment.
For further details on implementing these features, explore the PKI external CA documentation. You may also want to check out the latest updates in the Vault 2.0 release blog.